Techniques For Testing Website Security Using The Escaping Metacharacter Method
Teknik Menguji Keamanan Website Dengan Menggunakan Metode Escaping Metacharacter
DOI:
https://doi.org/10.21070/pels.v2i2.1223Keywords:
Cross Site Scripting, Information, Metacharacter, VulnerabilitiesAbstract
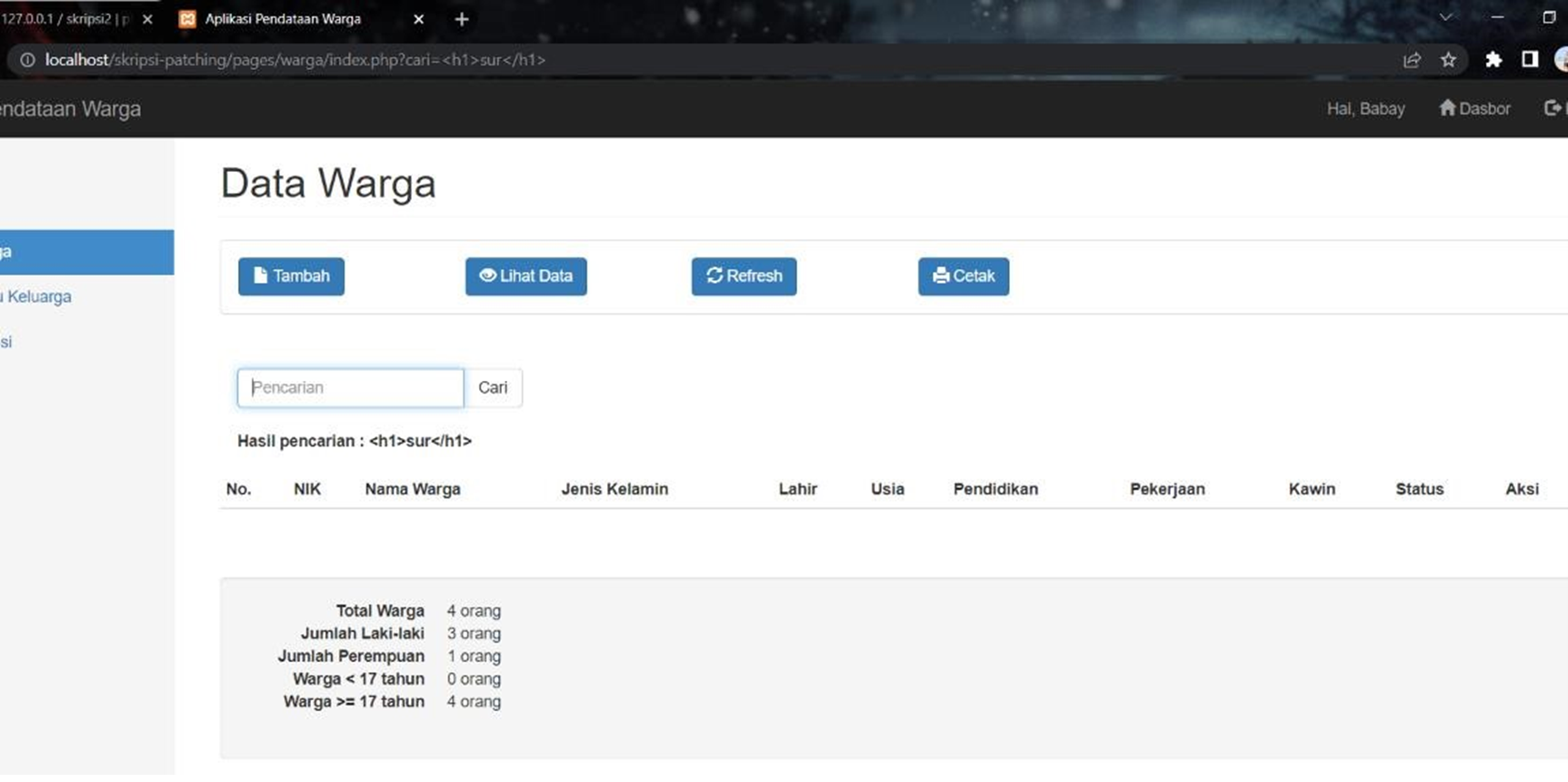
Information has become a very important need and has even become a basic need in this day and age. Much of the information available is confidential and not everyone has access to that information. CrossSite Scripting is a type of injection attack against a site by relying on weaknesses from the website or the user itself. Attackers try to steal data, confidentiality and website structure with certain commands through code scripting which is very contrary to the principles of information system security. So that the basic principles of information system security can be fulfilled, it is necessary to conduct research with the aim of finding loopholes and the effect of certain treatments for CrossSite Scripting attacks on websites under controlled conditions and closing the vulnerability gaps of the website. The research was conducted using the escaping metacharacter method which functions to convert special characters into HTML format. This method also functions as a filter on input so that the script that is injected by the user will not be executed by the browser and will be considered as normal input. From the results of the study, it shows that by entering certain characters or words as a rule (filter) which is the hallmark of the xss script, a pattern will be obtained which can later be used as a determinant of whether the input is really an ordinary string or script injection. The research contribution to be achieved is the importance of doing penetration testing on an information system for Agencies, Institutions and Companies, to always be able to recognize, analyze and respond to attacks on information systems and provide security and comfort to users of the information system.
Downloads
References
B. A. Wisnu and N. J. K. P, “Prediksi Serangan Scripting Lintas Situs Menggunakan Mesin Belajar Algoritma,” pp. 1–5, 2014.
K. Devi, “Mendeteksi Aplikasi Web Berbasis XSS Kerentanan,” 2017.
Yulianingsih, “Melindungi Aplikasi dari Serangan CrossSite Scripting (XSS) Dengan Metode Metacharacter,” 2017.
S. Xss, M. Firefox, Y. T. Wahyuni, and A. M. Shiddiqi, “Rancang Bangun Add-ons Deteksi Cross Site,” vol. 2, no. 1, pp. 1–4, 2013.
R. Pangalila, A. Noertjahyana, and J. Andjarwirawan, “Penetration Testing Server Sistem Informasi Manajemen dan Website Universitas Kristen Petra.”
Fietyata Yudha. A. M, “Perancangan Aplikasi Pengujian Celah Keamanan Pada Aplikasi Berbasis Web,” vol.2, 2018.
H. Aliyasa Almaj Duddin and A. Senja Fitrani, “IMPLEMENTASI METODE IDS IPS DALAM PENGAMANAN FORM INPUT TERHADAP SERANGAN SQL-INJECTION Dan XSS,” 2019.
Herman Tolle, S.M, “Peningkatan Keamanan Web Terhadap Serangan Cross Site Scripting (XSS),” 2008.
I Made Suartana, S. M, “Sistem Pengamanan Web Server Dengan Web Application Firewall (WAF),” vol.x, no.1, 2015, 42.
Johanes Indra Homenta. R. E, “Menganalisa Sistem Keamanan Jaringan Berbasis Intrusion Prevention System dan Honeypot Sebagai Pendeteksi Dan Pencegah Malware (Studi Kasus PT. Karya Mitra Nugraha),” 3-4, 2015.
Jhon Nicolas Siahaan, Y. M, “Aplikasi SMS Gateway Di PT. Mercaya Globe Sphere,” 4-5, 2013.
Gadhi Pranoto. R. D, “Rancang Bangun Aplikasi Terpadu,” vol2, 2016.
Dini Hariyati, R. A, “Pembangunan Sistem Informasi Rawat Jalan Berbasis Web Dengan Fitur Mobile Pada Puskesmas Tarok Kota Payakumbuh,” 2017.
Fauzan Masykur. F.P, “Aplikasi Rumah Pintar (Smart Home) Pengendali Peralatan Elektronik Rumah Tangga Berbasis Web,” 95, 2016.
Elisa Usada. Y. R, “Rancang Bangun Sistem Informasi,” 43, 2012.